How to use the HIPAA Policy Template
Creating and managing HIPAA security policies is critical for healthcare providers and other covered entities to protect patient information and comply with legal standards. To effectively create and manage HIPAA security policies, it's important to:
Step 1: Access the template
Access the HIPAA compliance policy template by clicking "Use template," which opens it in the Carepatron app's template editor. There, you can create customized policies and procedures that comply with HIPAA standards. You can also get a boilerplate policy PDF with a few customizable fields by clicking "Download," but you can't add more clauses to it.
Step 2: Identify covered entities and business associates
Ensure that all parties handling PHI, including healthcare providers and their partners, are identified, and their responsibilities under HIPAA security policies are clearly set out. A covered entity is an organization or individual who transmits patient data or is involved in transactions.
The scope of the policies includes any information in medical records and other relevant documents that can be used to identify an individual, which is created, used, or disclosed while providing healthcare services.
Step 3: Implement administrative safeguards
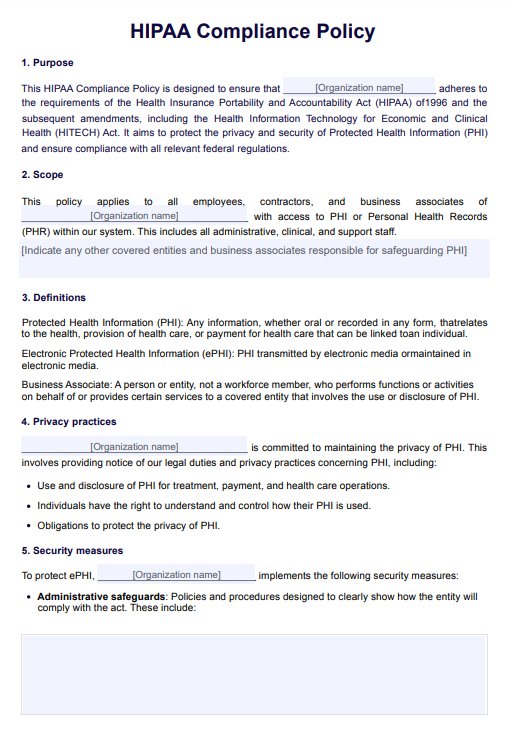
Assess risks to electronic media and PHI, specific to the organization. Develop appropriate procedures to limit access to PHI and control how it is used and disclosed. All policies should be designed with the primary goal of protecting patient information from unauthorized access, disclosure, alteration, or destruction.
For each section of the policies template, indicate these specific security measures (e.g. employee training programs on protecting PHI and reporting malicious software, conducting regular risk assessments to identify potential threats to the security of PHI, encryption, etc.)
Step 4: Establish a response plan
Establish a response plan for potential breaches, including a data backup plan and notification procedures for affected individuals and regulatory bodies. Indicate these measures in the relevant sections.
Step 5: Regularly review and update
Review the completed policy document to ensure each HIPAA policy has been comprehensively covered. Implement procedures for maintaining compliance with HIPAA policies, including regular audits and monitoring of policy adherence. Ensure mechanisms are in place to identify and mitigate any compliance gaps or weaknesses in the organization's PHI security.
Creating and managing effective HIPAA security policies requires a thorough understanding of the risks to PHI, a commitment to implementing comprehensive safeguards, and an ongoing effort to monitor and adjust policies as necessary.